Bexar: The chicken machine that doesn't make chickens
In Stravinsky’s The Rake’s Progress, Nick Shadow wheels out a “fantastic Machine” and demonstrates that it turns stones into bread. Tom Rakewell, desperate and gullible, believes it. He tries to market the machine to save mankind. It’s a fraud. The machine doesn’t turn stones into bread. The hidden compartment does the trick. The audience knows this. Tom doesn’t.
Bexar County has the opposite problem.
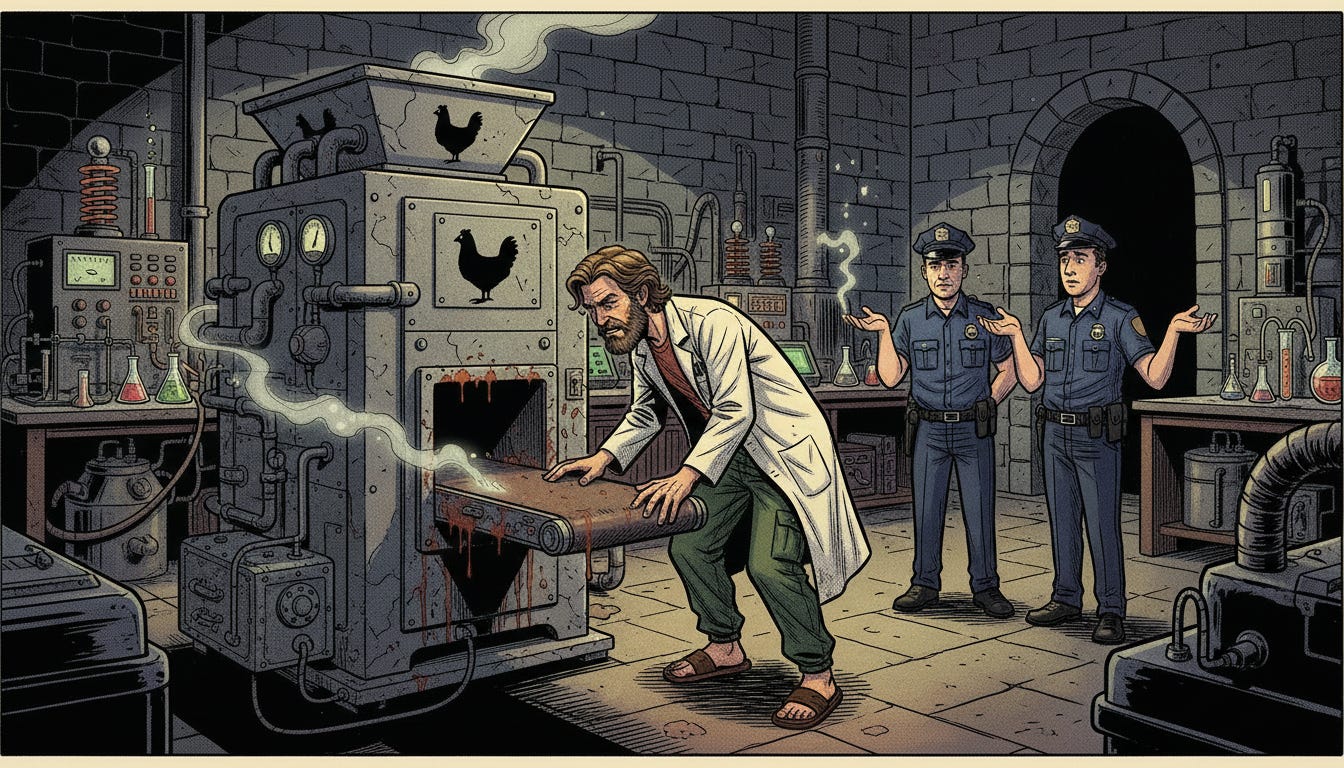
Here, the machine is real. It does exactly what it was built to do. And the argument being made — by people who should know better — is that maybe it didn’t.
A voter check-in system has one function. When a voter walks into a polling location, a poll worker looks them up in the electronic poll book, confirms their identity, and checks them in. That check-in is a ballot authorization. It is the gate through which a ballot is issued. No check-in, no ballot. Check-in, ballot. That is the entire purpose of the system. It doesn’t do anything else. It is a chicken machine. It makes chickens.
On February 18, 2026, someone ran the chicken machine 4,110 extra times.
Not by hand. Not at a polling location. Not during voting hours. Based on characteristics of the software used, it looks as if: after the polls closed, an actor with back-end access to the KnowInk poll book system injected 4,110 synthetic voter check-in records into the Bexar County Republican primary early voting file. The records were not sloppy. They were mathematically perfect — a single uniformly-spaced sequence with a gap of exactly 22,084.82189 between each consecutive record, spanning a range of 90.7 million ID numbers that falls entirely within a void in the Texas statewide voter database where no legitimate voter exists. The span divided by the gap equals exactly 4,109. A perfect integer. Zero remainder. That is not a glitch. That is a specification.
The 4,110 records were built from the identities of 735 real voters who had actually checked in that day — every one of them with a last name starting with A, B, or C, selected by alphabetical sort from the completed check-in list. Each of those 735 names was cloned either 5 or 6 times, in a split of exactly 300 and 435 — the unique algebraic solution to the constraint system. The algorithm cycled through all 735 names in alphabetical order, made five complete passes, then began a sixth pass that stopped at name 435. That voter’s wife, at position 436, got only five copies. The cutoff is surgical.
The fractional components of the fake State IDs — invisible to poll workers under normal display settings — functioned as a machine-executable deletion key. One database query filtering for non-integer IDs would return exactly 4,110 records and zero legitimate ones. Insert, authorize, delete. The ballots stay. The evidence disappears.
Except it didn’t disappear. The file was captured on February 19, before the cleanup was complete.
Now here is the question that should end every conversation about this:
Why would someone do all of that — and not take the chickens?
Think about what this operation required. Someone had to have access to the complete Texas statewide voter database to identify a 777-million-ID void where no registered voter exists. Someone had to wait for the polls to close and the final check-in list to be compiled. Someone had to write purpose-built software — not a spreadsheet formula, but compiled code, as proven by the IEEE 754 floating-point fingerprint in the gap cycle — that sorted 735 names alphabetically, solved a two-equation integer system, derived a precise spacing gap from the endpoint State IDs, generated 4,110 records with coordinated fake addresses, fake precinct numbers following a three-stage conditional branching algorithm, and fractional IDs designed for clean post-operation deletion. Someone had to inject those records into the poll book system through a back-end connection — likely through KnowInk’s ePulse platform, which is accessible from the open internet with nothing more than a username and password. And then someone replaced the entire February 18 file no more than a week later with a clean version.
That is an enormous amount of effort. It is an enormous amount of risk. Unauthorized access to an election system is a federal crime. Fabricating voter records is a federal crime. Every one of those 4,110 records is a separate count.
And the suggestion — the one that is supposed to be the reasonable position — is that whoever did all of this didn’t use it to produce ballots.
That the chicken machine ran 4,110 times, after hours, operated by someone who broke in, and produced no chickens.
This is the argument you have to believe to maintain that no ballots were affected: that a person or group with state-level database access, custom-written injection software, back-end credentials to the poll book system, and the operational sophistication to execute and then cover up a 4,110-record insertion — did all of it for nothing. Exposed themselves to decades of federal prison time for nothing. Built an elaborate deletion mechanism to hide evidence of nothing.
The check-in system is a ballot authorization system. That is its only function. You don’t hack into it at 2 AM, fabricate 4,110 algorithmically perfect records in the names of real voters, and then not take what the system is designed to produce. You don’t build a chicken machine, run it 4,110 times in the dark, and then argue about whether chickens came out.
The default position should be: the chickens came out.



Awesome forensic investigation and intelligence written in clear English that any literate American can comprehend, if they decide to read the evidence presented. Grateful thanks for you, Dr. Zark.
if you consider the results of stolen elections the gains to the criminals are greater than the risk. we ve run 5 consecutive national elections that have every conservative shaking their head's saying how the heck did he or she win? the fact that democrats have won 99.99999999 % of extended election counting kinda tells us who s cheating. the question is who will fix the problem before the next civil war? i don t think republican politicians are up to the challenge